How to Create Strong Passwords and General Password Guidelines too
 Strong password protection has become critical as we use the internet for just about everything, including shopping, Social Media and services such as online banking. My 70 year old mom refuses to get paper bank statements in case someone intercepts her mail yet she is completely at ease with online banking. Go figure! That said, I had a hard time staying calm when I discovered she was carrying her passwords with her, right next to her bank account numbers. Very bad idea!
Strong password protection has become critical as we use the internet for just about everything, including shopping, Social Media and services such as online banking. My 70 year old mom refuses to get paper bank statements in case someone intercepts her mail yet she is completely at ease with online banking. Go figure! That said, I had a hard time staying calm when I discovered she was carrying her passwords with her, right next to her bank account numbers. Very bad idea!
In addition to tips for creating sturdy passwords that are likely to stump hacking software, here are general guidelines to help protect online accounts and passwords.
- Create strong passwords:
- Use combinations of uppercase and lower case letters, numbers, punctuation and special characters.
- Strong passwords are 8 to 20 characters long – passwords over 9 characters are difficult for hacking software to crack.
- If you must memorize passwords, use the first letter of each word in a phrase and intersperse special characters. ie Humpty Dumpty – H&D&s&o&a&w&H&D&h&a&g&f
- Avoid usernames in passwords in any form (backwards, doubled etc).
- Don’t use obvious passwords such as names and numbers pertaining to you or your family. “Password1”, is one of the most commonly used passwords. “Monkey” and “0123456” are popular too. Stay far away from these.
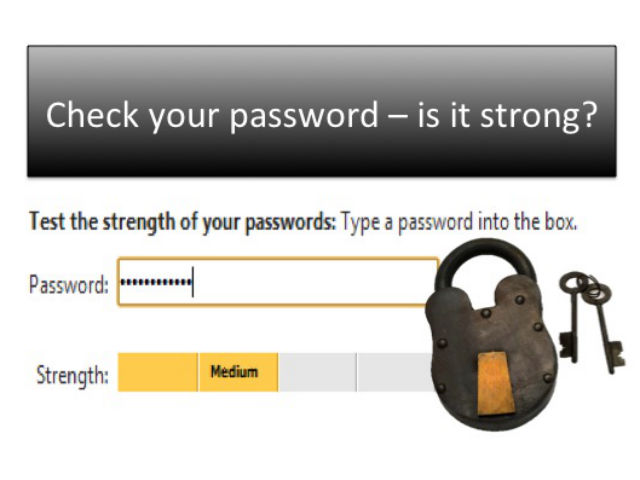
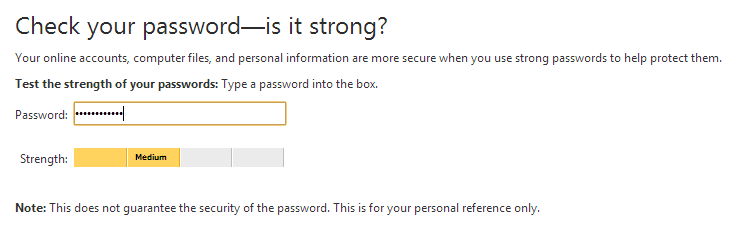
- Check the strength of your passwords by clicking on this password strength checker on the official Microsoft site.
- Keep your passwords private:
- Don’t store password lists in unencrypted computer documents. These lists can be accessed if computers are hacked.
- Avoid storing written passwords close to your computer.
- Pairing passwords with account names and numbers on paper or technology is risky but it’s worse if you carry that information with you. Purses, wallets, cell phones, tablets and computers are easily stolen and why be an easy victim?
- Refrain from storing passwords in cell phones. For additional security tips read, How to Secure your Smartphone.
- Do not share your passwords with others.
- Be cautious when an app asks you to enter a password to another site in order to use that app. I usually avoid such apps.
- Do not use the same logons and passwords for multiple accounts. Hackers will obtain passwords from sites that are easier to break into and will try those same passwords on more secure sites.
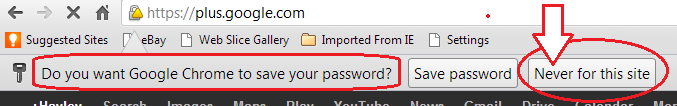
- Do not have your browser remember passwords for you
- Change your passwords regularly – suggested frequency is every 3 months. If that’s not realistic for you, change them as often as you can manage.
- If you have a long list of passwords, use Password Management Software or Biometrics to create unique and strong passwords and to remove the need to memorize a huge volume of passwords.
- 1Password, LastPass, KeePass, KeePassX, RoboForm and Firefox Sync are popular software managers.
Most users speak highly of them and claim they don’t know how they ever managed without them. I’ve avoided a password manager because I don’t like my confidential information being stored in the cloud but I’m about to test one out for my less critical passwords. I’m trying to decide between LastPass and Password1 so if you have an opinion about password managers, please share it with me.
- “Biometrics” is the use of personally identifiable anatomical data (ie fingerprint, iris or facial scans) to access property, computer networks, cell phones, computers, ATM machines and more. Biometric advocates are huge fans, but others claim biometrics are unreliable. After conducting a poll, participating in LinkedIn discussions and reading comments following an article, Keeping Track of Passwords and Usernames, I abandoned my attempt to try a fingerprint reader.
Until next time … Stay Cyber Safe!







we use 1password and really like it. thanks for the great article hayley.
You’re welcome, Jill. Thanks for letting us know you use 1password. I will assume you like it!
Great tips. I like that password strength checker tool.
I’ve used sites like http://random.pw to help me create strong, memorable passwords. Something I can easily remember, but has all the crazy numbers and special characters. It also has a password strength checker.
I appreciate the kind words and the site to create passwords from. Thanks, Joel.
I use a great password manager. It not only has two factor authentication and client-side encryption, but I can use it on any browser and it provides virtual email addresses I can use for an extra layer of privacy and spam control. It creates and stores not only strong passwords, but also usernames too.
http://kemesa.com. There’s a free version but its probably not going to be enough if you use it regularly.
Thank you for your input!
Good set of guidelines, and I was pleased to see that one old guideline (“don’t write down passwords”) was missing.(These days people have too many passwords, they HAVE to write them down – just don’t write them down in an obvious way or in an obvious location.
One guideline that I think was missing is to have classes of passwords. Since every site seems to require one these days, I have a couple reasonably secure passwords I use for sites that have no personal info (e.g. newspaper web site), and I don’t worry about changing them; then a totally different schema for sites with personal info, and a third schema for work.
Your suggestion regarding having different classes of passwords is excellent. I actually do that myself but didn’t think to include it in the article.
Thanks Allison!
Excellent advice, Hayley. I have a hard time remembering the passwords I do have, I think I would go bonkers if I had to keep changing them. But I will. The thought of being hacked sounds awful. Thanks for keeping us safe.
Carpool Goddess – I also go bonkers from changing my passwords. I prioritize password changes for those sites that have sensitive personal and financial information and I don’t worry much about the others.
A timely posting Hayley! A simple trick is to do letter-number replacements such as 1 for 1, 4 for “for” or “fore”, 8 for “ate”, etc, but not to do it consistently.
Someone also shared a tip with me about answering password reset questions that I can pass on. “Be a politician” they said. “Don’t answer what they are asking, but answer what you want to answer.” For example if the challenge question is “What was the make and model of your first car?” answer something totally unrelated like “spare ribs”. It makes it tougher to remember the correct response, but avoids bad guys from using social engineering techniques to guess the answers. (see http://privacyref.com/wordpress/2012/08/13/social-engineering-and-challenge-questions/)
Bob,
Thank you for your excellent suggestions. I’d like to second your point of not using number-letter replacements too often as hacking software takes those into account and consistent usage can reduce the effectiveness of a password.
I hope readers of this article will read and more importantly, follow your advice in your article regarding Challenge Questions and Social Engineering. Many people are overly generous with the private information they share on Social Media and it is indeed easy to answer many of the security questions in your article by doing public searches.
Thanks again.
Hayley
I try to explain to people how important it is to frequently change passwords. They are often reluctant. Your piece explains the risk so well.
Thanks, BH Mom.