We Don’t Cover Stupid! How to protect sensitive data.
 “We don’t cover stupid” is a reminder that ignorance and lack of expertise have become unacceptable excuses for technological negligence. This entertaining but reasonable statement was made by an insurance company who is suing for reimbursement of a payout after learning an insured healthcare provider failed to take appropriate security measures to protect online patient medical records. The provider’s carelessness resulted in confidential patient information being made accessible to the public via Internet searches and the insurance company asserts that healthcare providers must be held accountable for adhering to a basic level of responsibility when entrusted with such information. As much as I dislike the idea of an insurance company weaseling out of paying a legitimate claim, I have to agree with them on this one!
“We don’t cover stupid” is a reminder that ignorance and lack of expertise have become unacceptable excuses for technological negligence. This entertaining but reasonable statement was made by an insurance company who is suing for reimbursement of a payout after learning an insured healthcare provider failed to take appropriate security measures to protect online patient medical records. The provider’s carelessness resulted in confidential patient information being made accessible to the public via Internet searches and the insurance company asserts that healthcare providers must be held accountable for adhering to a basic level of responsibility when entrusted with such information. As much as I dislike the idea of an insurance company weaseling out of paying a legitimate claim, I have to agree with them on this one!
Beyond cyber insurance companies, businesses are held accountable for reasonable practices by entities such as the Federal Trade Commission. Businesses are expected to minimize risks to those who access their products and services and when they don’t do this, they can expect to pay hefty fines and to suffer from reputation damage, lawsuits and other general losses. While this article is geared toward businesses, it’s simultaneously intended to impart an important message to everyone: Advanced technology is integrated into our daily lives and it is our responsibility to acquire a fundamental education to minimize the ever increasing risks and related damages to ourselves and to others. Not taking steps to protect ourselves is a matter of personal choice, but using lack of knowledge as an excuse when causing harm to others is unacceptable.
To understand the magnitude of cyber breaches, see the Identity Theft Resource Center’s Data Breach Report that is updated every Tuesday. Between January 1, 2015 and June 16, 2015, 361 breaches exposing over 107,000,000 records in the Banking/Credit/Financial, Business, Educational, Government/Military and Medical/Healthcare sectors were reported. The actual numbers are most likely to be significantly higher because some breaches remain unreported and the full extent of others is unknown.
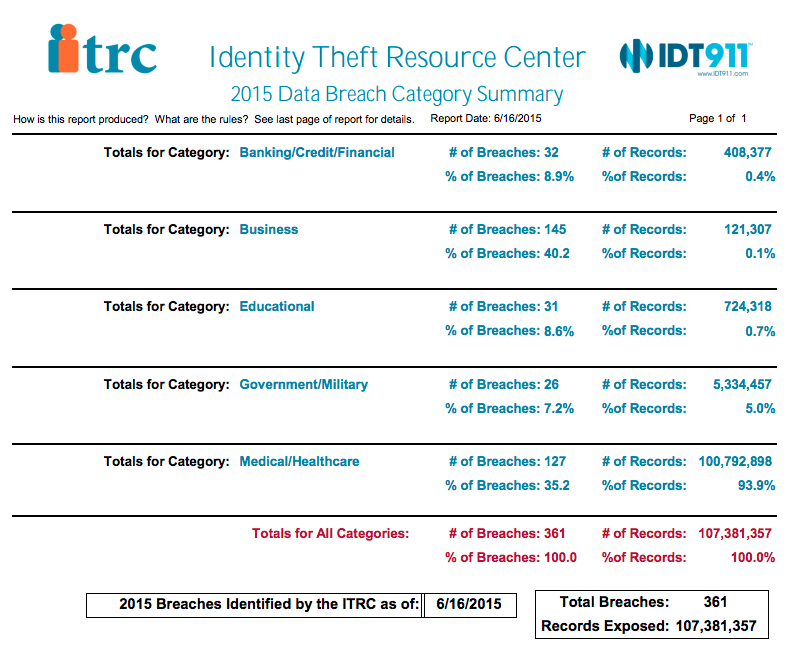
Summary of 2015 Data Breaches to date from a 77 page report from Identity Theft Resource Center (January 2015 – June 17, 2015)
Rapidly increasing cyber crimes are frustrating and damaging however, it is possible to reduce the number and severity of these breaches by taking steps to reasonably protect sensitive data. In fact, “the touchstone of the FTC’s approach to data security is reasonableness: a company’s data security measures must be reasonable in light of the sensitivity and volume of consumer information it holds, the size and complexity of its data operations, and the cost of available tools to improve security and reduce vulnerabilities.” This sounds vague however there are rules and documentation that elaborate and expand on this principal.
The Gramm-Leach-Bliley Act requires companies that offer consumers financial products or services such as loans, financial or investment advice, or insurance to explain their information-sharing practices to their customers and to safeguard sensitive data. The FTC offers tips for compliance.
The Red Flags Rule helps businesses identify suspicious patterns and reduce or prevent the expensive consequences of identity theft via the implementation of a written Identity Theft Prevention Program designed to detect the early warning signs – or red flags – of identity theft in day-to-day operations. The FTC’s How To Guide for Business provides additional valuable information.
A component of the Red Flag’s Rule is the Safeguards Rule which requires financial institutions to secure customer records and information. But the law defines “financial institution” broadly to cover many businesses who might not describe themselves that way and therefore each business should review the details and take advantage of the general information that is likely to help most businesses put a sound plan in place to protect both themselves and their customers.
The Federal Trade Commission (FTC) provides valuable free resources to assist businesses with important security aspects including Physical Security, Electronic Security, Password Management, Laptop Security, Firewalls, Wireless and Remote Access, Digital Copiers, Detecting Breaches, Employee Training and more. Their Business Guide for Protecting Personal Information is especially helpful.
The essence of the FTC expectations for those that keep sensitive employee and customer information is:
- Know exactly what type of personal information is stored.
- Store only what is needed and dispose of the rest securely.
- Secure and protect all personal/sensitive information.
- Have a plan in place for incident response.
Consumers are entitled to reasonable expectations of being protected by the entities they share their personal information with and perceptions of how consumers are protected before, during and after a breach can make or break a business. There is no denying the challenges, the expense and the time investment imposed on businesses to protect their customers. But since it’s not a matter of if but a matter of when when it comes to breach attempts, the time is now to make or review such a plan and to practice prevention instead of cure!
Until next time, … Stay Cyber Safe.






Thank you Hayley for this helpful and insightful piece. I look forward to receiving your next one.
Appreciate the acknowledgement, Cathy. It’s always nice to know my articles are being read. 🙂