Electronic Trails and Footprints – Privacy Pros and Cons
After buying a dishwasher from a local appliance store, I purchased an anniversary gag gift from the Hustler store for friends that love a good prank. However, it was my friends who ended up with the last laugh after an employee at the appliance store stole the credit card numbers of many customers, including mine. I couldn’t have been more embarrassed as I tried to explain to the investigating detective that the dishwasher and awkward Hustler store purchases were legitimately made by me but the extravagant restaurant charges and abundant liquor store charges were not mine!
We voluntarily sacrifice privacy when we create digital footprints as we announce our behaviors and spending habits by using technology, credit cards and loyalty cards in our quest for convenience and to save money. Electronic footprints may reveal misdeeds as well as other innocent information we have unintentionally shared.
We create these footprints with social media and from technologies such as credit cards, GPS systems, car computers, internet surfing, loyalty cards and RFID systems (Radio frequency identification that transmits the identity of an object or person wirelessly using radio waves). Card issuers, affiliate businesses, individuals, lawyers, and law enforcement can get access to this information and it can be used for or against us in multiple ways.
Recalls:
Tracking can provide an important consumer benefit.
- Tracking can be critical for consumer safety when it becomes necessary to notify consumers regarding defective products such as car seats, toys or cars.
- Tracking of food and drug purchases have been instrumental in determining the cause of health outbreaks as well as serving as a means to notify pertinent parties. Food and drug recalls from loyalty card purchases have saved lives and prevented spread of contamination in cases of tainted medications and foods.
Marketing:
Tracking for marketing purposes is a double-edged sword with both pros and cons for the consumer. “Cookies” are small pieces of information sent by a web server to a web browser, to enable the server to collect information. The cookies build a demographic profile by keeping track of the browsing behavior and target interests of users; trends and patterns are used to understand a customer’s purchase behavior and habits and to respond accordingly.
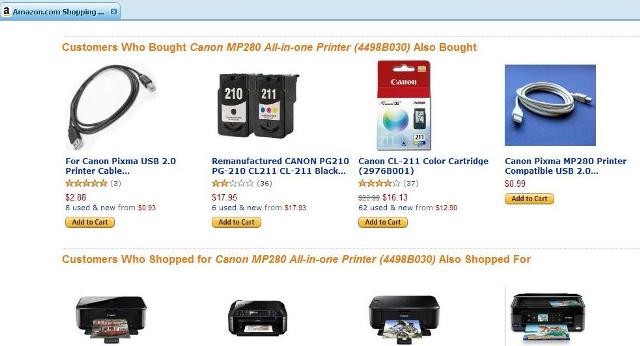
- Demographic profiles and browsing history can be used to enhance a user’s on-site experience. Companies such as Amazon.com track on line behavior and purchases to suggest related products that may be of interest. For example, on a recent printer purchase for my dad, Amazon.com saved me research time by letting me know that customers who purchased that printer also purchased specific ink cartridges. If I’d paid closer attention to Amazon’s suggestions, I wouldn’t have forgotten the printer cable which I needed to connect the printer to dad’s computer.
- Companies can encourage spending by offering incentives to customers based on their interests and needs.
For example, supermarkets send customized coupons to their customers. Frequent flyer and frequent buyer programs reward consumers for their loyalty and encourage consumers to spend more or to make as many charges as possible on their credit card to earn miles, bonus points or other incentives. This is a mutually beneficial relationship. I rarely pay to travel to international destinations as I usually use miles earned to purchase plane tickets.
- Visitors that click on advertisements are sent a cookie to analyze advertising effectiveness and to manage the relationship with affiliate sites. Personal data may be provided to affiliate companies who also want to use the information to generate revenue.
While certain offers may result in cost savings and identification of useful new targets to spend money on, they can be annoying as we are inundated with unsolicited offers and information. Additionally, some of this information may be used against us. For example, heavy purchasing of certain medications could be used as an assumption of a medical condition and could lead to health insurance issues such as higher rates or excluded medical conditions. There are cases where expenditure history has worked against the consumer in legal situations. (See legal Issues below)
Personal Motives: (Extramarital Affairs, Alimony and Palimony Situations)
- A person’s spending behaviors may imply they can afford the alimony or palimony payments they are shirking.
- One may learn of an unfaithful partner after discovering suspicious charges on a card for lingerie and gift items or hotel and restaurant charges the other partner had no knowledge of. Cell phone records may also establish a behavior pattern or identify a potential issue.
Legal Issues:
-
Electronic tracks can establish where someone was or where someone wasn’t. This extends beyond credit cards to RFID Tags and Keys, cell phones, a car’s GPS unit or computer. Just like credit cards, RFID Tags can provide an accurate record of the dates and times they are scanned. In the mid-Atlantic and northeastern part of the United States, many states use electronic windshield tags that allow scanners to charge an account in order to speed up the process of passing through toll plazas. For most people, this serves as a helpful time saver and convenience strategy. That said, lawyers can use this location information to dispute alibis of dishonest spouses, lovers, employees and criminals.
Law Enforcement and Homeland Security:
- Credit card transactions contain a date, time and location for each purchase.
- Records may be subpoenaed to help track a suspect or a victim. RFID data used on items such as hotel or office building entrance keys or EZ Scans for toll roads and border crossings can also identify locations of victims and suspects. GPS Systems and Cell phones with GPS locators in them may be used to trace the location of suspects (criminal or terrorist) and victims.
- The interest of Homeland Security is activated by credit card expenditures that may relate to terrorist activities. Terrorists can also be tracked by the technology they are using such as cell phones and browsing history.
Fraud Detection:
- Certain expenditures may be indicative of fraud therefore credit card companies vigilantly monitor purchases in order to reduce and to cut off fraud as soon as possible. This is essential to businesses but can sometimes prove to be an inconvenience to consumers when a card cannot be used until the card issuer is certain the expenditures being made are legitimate.
Risk Management:
Laws require banks to provide privacy policies to cardholders but the law does not restrict what the card issuers can do with information that is gathered internally.
- Purchase behaviors can be used to determine creditworthiness. Exceeding credit limits and not paying credit card bills on time may indicate a card holder is at risk for not paying bills or for filing for bankruptcy.
- Unusual spending habits such as a sudden large amount of high cost purchases or use of multiple cards rarely used before may also spark concern and limit success for obtaining additional cards or loans.
- Purchase data may be used as a basis for increasing or reducing credit limits and also for increasing interest rates for customers who are considered higher risk based upon what they shop for and where they shop for it. A lawsuit was filed against CompuCredit for lowering credit limits on customers who shopped at certain establishments or used services including automobile tire retread and repair shops, bars, nightclubs, pawn shops, marriage and personal counselors and massage parlors.
Health:
- After filling a recent allergy medication prescription, my son started to receive solicitations for Asthma research as well as suggestions from his insurance company regarding Asthma related testing. My son does not have Asthma and I am concerned that this incorrect analysis of his purchase behavior could result in a negative consequence such as a higher medical insurance rate or disqualification from certain professions. In spite of calls to the insurance company and charity, my battle is not over as my son continues to receive unwarranted Asthma related information.
- Confidential health information could covertly be used against a person when it comes to potential employment and investment opportunities.
How to prevent tracking:
- Protect against unauthorized use of your information by using strong passwords and keeping those passwords private.
- Always sign out after using a shared computer.
- Do not use loyalty cards or programs
- Delete all tracking cookies and browsing history from your computer and similar devices. Cookies can be removed by following directions in your Internet browser’s “help” file.
- Use cash instead of credit cards
- Opt out of having personally identifiable information being used. For example, we are often provided privacy policies by businesses and organizations. Read and exercise opt out options when you receive such notifications from financial institutions and vendors. You can usually opt out of subscriptions and emails as you receive them.
- Understand the capability of all technology you use so that you can turn off tracking mechanisms in items such as cell phones, GPS cameras and GPS systems. You can also contact manufacturers for product specific guidance or technical support to do this.
As long as tracking simultaneously works for and against us, the struggle will continue as we strive to find balance in this world of diminishing privacy. We need to carefully weigh risks and inconveniences versus benefits and conveniences of leaving footprints behind as we decide how far we’re willing to go in our quest to keep our personal lives and behaviors private.