Cyber Security: 2 ways to Protect yourself, your Family and your Community – Part I
I recently completed two Cyber Security classes provided by TEEX, a Training and Education Division of the U.S. Department of Homeland Security. I wanted to learn how local communities prepare for and respond to cyber threats and I hoped the training would allow me to make a positive contribution to my readers and my community. The training was excellent. Clearly, I can make a difference, and so can you!
The Anatomy of a Cyber Attack
Cyber attacks come in many forms. Attacks can be unstructured and random or they can be highly structured, organized and intentional. A “virus” requires human assistance to spread while a “worm” is automated as it seeks out vulnerabilities and spreads quickly on its own. “Trojan Horse” attacks may appear to be helpful but have hidden malicious code. An example of this was seen years ago when people downloaded pretty screensavers and then discovered they had downloaded malware which slowed down their computers and forced those computers to participate in a Denial of Service Cyber Attack.
Cyber attacks can go into action immediately or they can remain dormant for a while until a certain date or instance of vulnerability presents itself. (Time/Logic Bomb or Backdoor/Trapdoor) The name or type of attack is not what matters. When it comes to Cyber attacks, what matters is being prepared, being aware and then having the knowledge to deal with the situation or to get the right type of help as soon as possible to reduce or eliminate negative consequences.
Your Relationship to Cyber Attacks
Question: What is impacted by cyber (computer systems and networks)?
Answer: Everything!
- Your homes, offices, schools and communities
- Critical infrastructures (emergency services, communication, power, water, banking, transportation, hospitals, oil and gas)
- Industry
- Government
Question: How can you make a difference, especially if you don’t work in public service?
Answer: By getting informed.
- Since the ignorance or mistake of a single person can cause harm to many, the more educated we are, the safer and better off we all will be. Gaining knowledge may help you recognize important warning signs and guide you to react appropriately. Let me explain …
1. Don’t become a victim of phishing at home, school or work
By now, you’ve likely received a phishing email or two. I get several a week. Mine have claimed to be from Bank of America, America On Line, Twitter, Chase Bank, UPS and Paypal, to name a few. Initially, they were clearly fraudulent, but recently, many are appearing more legitimate and professional and therefore more dangerous.
Clicking on a malicious email link or downloading a bad attachment can ruin a computer, infect a network and lead to financial and identity theft. At home, you and your household members are at risk. At work, this number can multiply quickly as it impacts other employees and customers of that business. Imagine what type of damage could occur after clicking on a malicious link or downloading a virus on a hospital or bank computer and network. The breach of privacy and potential financial loss could be huge. Even worse, imagine what damage a cyber attack can do to critical infrastructure! Having no electricity or transportation or communication as a result of a cyber attack can have detrimental consequences.
We must all be vigilant and know how to avoid phishing schemes at all times. Awareness should begin at home and continue everywhere else. We must think carefully about any link we click on regardless of who it appears to come from. For more details, read How to Avoid Phishing Scams.
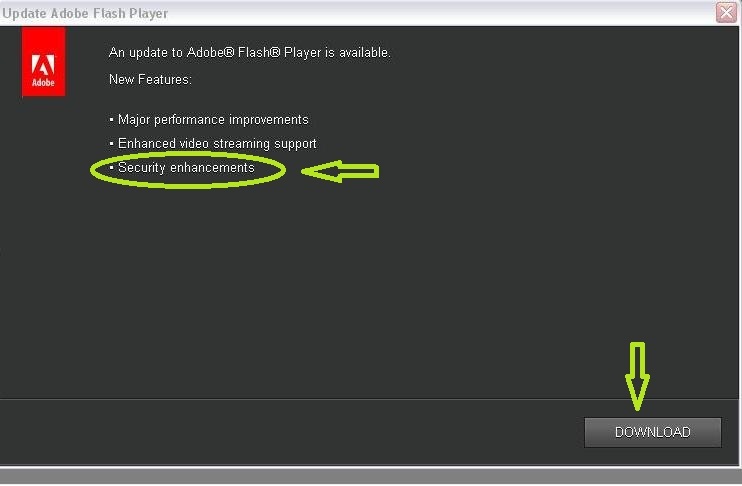
2. Keep virus protection current and install patches and updates at home and at work
Use good virus protection. Run virus scans regularly and always keep the software updated.
- Do not ignore messages on your computers and cell phones that ask you to update your system and your software as these updates often include important security corrections. Install updates and patches promptly to stay protected against security threats.
- Discuss Cyber Safety with all family members so all family members consistently take the necessary steps to protect themselves and therefore each other, especially when using the same network.
- Some businesses have departments to handle virus protection and updates for you. But, if they don’t, discuss this with your employer to see the best way to consistently handle this at work.
Until I attended the training, I didn’t realize how far reaching the consequence of phishing could be. I’ve never clicked on a phishing email link and I’ve accidentally assumed a legitimate link was not okay. But I’d rather err on the side of caution. If you have any comments or questions about this, please ask away.
Read Part II of this article for less obvious but important suggestions to keep your family, your household, your work community and of course, yourself, out of cyber trouble!
Until next time… Stay Cyber Safe!
* This article was updated on 9-12-12 to include links to Part II